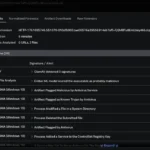
In this article we look at using PowerShell maliciously while evading detection.
Recent Posts
- GovWare 2025 Security Operations Centre
- GovWare 2025 Security Operations Centre
- From Detection to Deep Dive: Splunk Attack Analyzer and Endace for GovWare 2025 Security
- From Detection to Deep Dive: Splunk Attack Analyzer and Endace for GovWare 2025 Security
- Unmasking Attacks With Cisco XDR at the GovWare SOC