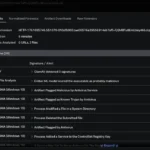
Local File Inclusion (LFI) Local File Inclusion (LFI) explained with examples, and learn how to perform security testing for LFI vulnerabilities. Introduction The intent of this document is to assist with web app security assessments engagements by consolidating research for LFI testing techniques. LFI vulnerabilities are typically discovered during application assessments or penetration testing using the techniques contained within this document. What is a Local File Inclusion (LFI) vulnerability? Local File Inclusion (LFI) allows an attacker to include files on a server through the web browser. This vulnerability exists when a web application includes a file without correctly sanitising the input, allowing and attacker to manipulate the input and inject path traversal characters and include other files from the web server. The following is an example of PHP code vulnerable to local file inclusion. Identifying LFI Vulnerabilities LFI vulnerabilities are typically easy to identify and exploit. Any script that includes a file from a web server is a good candidate for further LFI testing, for example: /script.php?page=index.html A security consultant would attempt to exploit this vulnerability by manipulating the file location parameter, such as: /script.php?page=../../../../../../../../etc/passwd The above is an effort to display the contents of the /etc/passwd file on a UNIX / Linux based system. Below is an example of a successful exploitation of an LFI vulnerability on a web application: PHP Wrappers PHP has a number of wrappers that can often be abused to bypass various input filters. PHP Expect Wrapper PHP expect:// allows execution of system commands, unfortunately the expect PHP module is not enabled by default. php?page=expect://ls The payload is sent in a POST request to the server such as: /fi/?page=php://input&cmd=ls Example using php://input against DVWA: Request: Image description: POST request using php://input Response: Image description: The output from the command “ls” is rendered above the DVWA banner. PHP php://filter php://filter allows a pen tester to include local files and base64 encodes the output. Therefore, any base64 output will need to be decoded to reveal the contents. An example using DVWA: vuln.php?page=php://filter/convert.base64-encode/resource=/etc/passwd Image description: Image showing the base64 encoded text at the top of the rendered page Base64 decoding the string provides the /etc/passwd file: Image description: An image showing the base64 decoded output from /etc/passwd on a UNIX / Linux system php://filter can also be used without base64 encoding the output using: ?page=php://filter/resource=/etc/passwd Image description: An image showing the output from /etc/passwd on a UNIX / Linux system using php://filter PHP ZIP Wrapper LFI The zip wrapper processes uploaded .zip files server side allowing the upload of a zip file using a vulnerable file function exploitation of the zip filter via an LFI to execute. A typical attack example would look like: Create a PHP reverse shell Compress to a .zip file Upload the compressed shell payload to the server Use the zip wrapper to extract the payload using: php?page=zip://path/to/file.zip%23shell The above will extract the zip file to shell, if the server does not append .php rename it to shell.php instead If the file upload function does […]
Recent Posts
- GovWare 2025 Security Operations Centre
- GovWare 2025 Security Operations Centre
- From Detection to Deep Dive: Splunk Attack Analyzer and Endace for GovWare 2025 Security
- From Detection to Deep Dive: Splunk Attack Analyzer and Endace for GovWare 2025 Security
- Unmasking Attacks With Cisco XDR at the GovWare SOC