A tidal wave of internet traffic slammed into Microsoft Azure last month… and the company barely flinched.
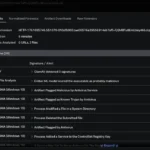
Microsoft has confirmed that Azure blocked a 15.72 terabit-per-second (Tbps) distributed denial-of-service attack on Oct. 24, an assault so large that it set a new record for cloud-based DDoS incidents. The target was a single endpoint in Australia, but the traffic tsunami came from more than 500,000 IP addresses spread across multiple regions.
Sean Whalen, Azure Security senior product marketing manager, described the scale clearly in Microsoft’s blog post, writing: “On October 24, 2025, Azure DDOS Protection automatically detected and mitigated a multi-vector DDoS attack measuring 15.72 Tbps and nearly 3.64 billion packets per second (pps). This was the largest DDoS attack ever observed in the cloud and it targeted a single endpoint in Australia.”
Aisuru botnet behind the blast
Microsoft traced the incident to the Aisuru botnet, a Mirai-derived IoT malware strain known for pushing attacks to extreme scales.
“The attack originated from Aisuru botnet. Aisuru is a Turbo Mirai-class IoT botnet that frequently causes record-breaking DDoS attacks by exploiting compromised home routers and cameras, mainly in residential ISPs in the United States and other countries.” Whalen confirmed in the blog.
The attack relied on fast, repetitive bursts of UDP packets that used minimal source spoofing and randomized ports, making it easier for providers to trace and enforce filtering. According to Microsoft, its worldwide network of scrubbing centers absorbed and cleaned the malicious flow in real time, keeping Azure workloads online throughout the event.
DDoS attacks are scaling with the Internet itself
Aisuru has been on a streak of headline-making bursts. Cloudflare linked the same botnet to a 22.2 Tbps attack earlier this year, while security researchers from Qi’anxin previously attributed an 11.5 Tbps strike to the group.
Experts warn that as home internet speeds get faster and more smart devices fill our homes, the potential for even larger attacks continues to grow. “Attackers are scaling with the internet itself,” Whalen noted. “As fiber-to-the-home speeds rise and IoT devices get more powerful, the baseline for attack size keeps climbing.”
With online traffic expected to spike during end-of-year shopping periods, Microsoft is urging organizations to review their defenses now. The company cautions organizations not to wait until an attack is underway before testing their defenses, urging regular simulations and operational drills.