Generative AI has rapidly evolved across every industry — and cybersecurity is no exception. As organizations continue to explore AI-driven solutions, foundational models have emerged as a powerful backbone for intelligent automation. These are large-scale models trained on vast datasets to perform a wide variety of general tasks, and they can be fine-tuned to specialize in specific domains.
The Cisco Foundation AI team has released a model on Hugging Face that’s fine-tuned on an 8-billion-parameter Llama model, specifically optimized for security use cases. This model demonstrates how enterprises can benefit from local deployments — especially in industries where data privacy, compliance, and regulatory constraints prevent the use of public cloud AI systems.
At the GovWare Conference, we showcased a proof of concept built on top of this Cisco-fine-tuned model. The goal was to explore Agentic AI — the concept of creating autonomous AI agents that can take action, reason about their tasks, and collaborate to achieve outcomes.
In future events, we plan to demonstrate the full potential of this model in production environments. For now, our proof of concept uses a Jupyter Notebook implementation that loads the model and introduces Agentic AI capabilities designed for Security Operations Centers (SOCs).
The Vision: Agentic AI in Security Operations
Imagine a SOC environment where each AI agent has a specific role — one might triage alerts, another might investigate incidents, and another could summarize threat intelligence. These agents work in harmony to accelerate the workflow of human analysts.
In our demo, we developed an AI agent responsible for investigating security incidents. Here’s how it works:
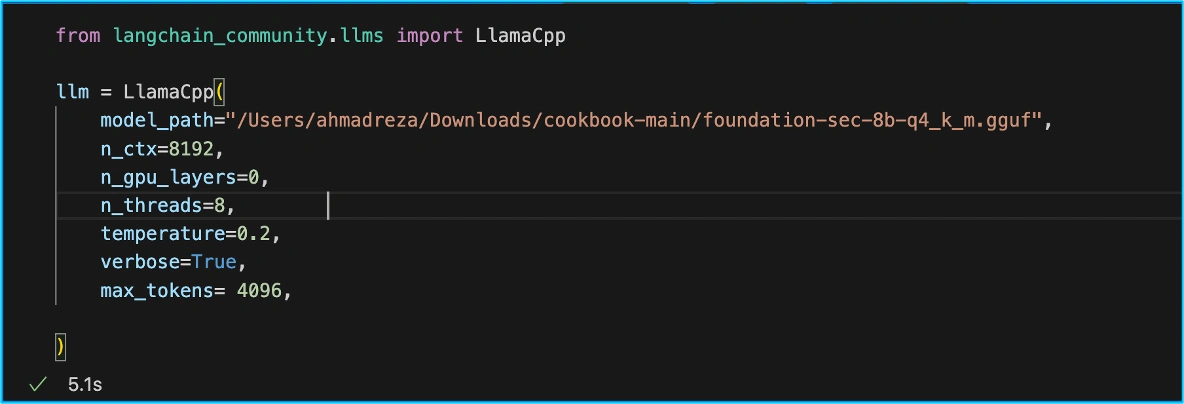
1. Model Initialization: We begin by loading a quantized version of the Cisco fine-tuned Llama model. This reduces resource requirements while maintaining strong inference performance.

2. Tool Creation: The AI agent is equipped with a set of tools — essentially, Python functions it can call to perform specific tasks.
- get_investigation_data: Extracts all observables (such as IPs, hostnames) from an incident, runs an investigation inside Cisco XDR, and summarizes the results.
- read_incident_summary: Reads all events from an incident and compiles a clear, concise summary of the findings.

3. Agent Initialization: We initialize the AI agent with conversation memory and give it access to the tools created in Step 2. This allows the agent to remember context and use the tools intelligently during its workflow.

4. Running the Investigation: Acting as a virtual SOC analyst, the agent receives user input — for example, a command to investigate a particular incident. The agent then runs the investigation, gathers data, and summarizes the results.

5. Agentic AI in Action: Because the agent has tool access, it knows when and how to execute the investigation functions. The output (shown in blue during the demo) contains all the indicators returned by Cisco XDR in JSON format.
The agent then interprets this data, reasons over it, and produces a final summary of the investigation — showing how Agentic AI can streamline SOC workflows by automating complex, multi-step investigative processes.

Here is an example of the Detections for the Incident in Cisco XDR.

The analyst can easily pivot into the Investigation for a visual representation.

Final Thoughts
This proof of concept demonstrates the transformative potential of Agentic AI in cybersecurity. By combining Cisco’s Foundational AI model with autonomous agent frameworks, we can empower SOC teams to work faster, smarter, and with greater precision — turning what used to be hours of manual investigation into minutes of automated insight.
Check out the other blogs by my colleagues in the GovWare SOC.
About GovWare
GovWare Conference and Exhibition is the region’s premier cyber information and connectivity platform, offering multi-channel touchpoints to drive community intel sharing, training, and strategic collaborations.
A trusted nexus for over three decades, GovWare unites policymakers, tech innovators, and end-users across Asia and beyond, driving pertinent dialogues on the latest trends and critical information flow. It empowers growth and innovation through collective insights and partnerships.
Its success lies in the trust and support from the cybersecurity and broader cyber community that it has had the privilege to serve over the years, as well as organisational partners who share the same values and mission to enrich the cyber ecosystem.
We’d love to hear what you think! Ask a question and stay connected with Cisco Security on social media.
Cisco Security Social Media