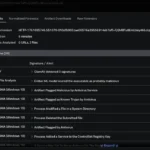
Microsoft has released its October 2025 Patch Tuesday updates, addressing 172 security flaws, including six zero-day vulnerabilities. Among these, eight are rated “Critical,” consisting of five remote code execution bugs and three elevation of privilege issues.
The breakdown of the patched vulnerabilities is as follows: 80 elevation of privilege, 11 security feature bypass, 31 remote code execution, 28 information disclosure, 11 denial of service, and 10 spoofing vulnerabilities. Microsoft’s tally excludes fixes rolled out earlier this month for Azure, Mariner, and Edge.
This week also marks the end of free security updates for Windows 10, with this being its final Patch Tuesday. Users who wish to continue receiving updates can purchase Extended Security Updates (ESU) — one year for consumers and up to three years for enterprises. Details on non-security updates are available in the Windows 11 KB5066835 and KB5066793 releases.
Six zero-days patched
Two publicly disclosed zero-day flaws were addressed in Windows SMB Server and Microsoft SQL Server, while three exploited vulnerabilities were also fixed.
CVE-2025-24990 – Windows Agere Modem Driver Elevation of Privilege Vulnerability
Microsoft removed the vulnerable Agere Modem driver (ltmdm64.sys) that allowed attackers to gain administrative privileges. “Microsoft is aware of vulnerabilities in the third party Agere Modem driver that ships natively with supported Windows operating systems,” the company stated. “The driver has been removed in the October cumulative update.” Removing the driver will disable related Fax modem hardware. The flaw was credited to Fabian Mosch and Jordan Jay.
CVE-2025-59230 – Windows Remote Access Connection Manager Elevation of Privilege Vulnerability
A flaw in Windows Remote Access Connection Manager, exploited to gain SYSTEM privileges, was corrected. “Improper access control in Windows Remote Access Connection Manager allows an authorized attacker to elevate privileges locally,” Microsoft explained, adding that exploitation requires “some measurable amount of effort.” The issue was attributed internally to the Microsoft Threat Intelligence Center (MSTIC) and Microsoft Security Response Center (MSRC).
CVE-2025-47827 – Secure Boot bypass in IGEL OS before 11
Microsoft patched a Secure Boot bypass affecting IGEL OS. “In IGEL OS before 11, Secure Boot can be bypassed because the igel-flash-driver module improperly verifies a cryptographic signature,” the company noted. The flaw, discovered by Zack Didcott and publicly disclosed on GitHub, allowed an attacker to mount a crafted root filesystem from an unverified image.
Publicly exploited vulnerabilities
CVE-2025-0033 – AMD RMP Corruption During SNP Initialization
This flaw affects AMD EPYC processors using Secure Encrypted Virtualization – Secure Nested Paging (SEV-SNP). “It involves a race condition during Reverse Map Table (RMP) initialization that could allow a malicious or compromised hypervisor to modify RMP entries before they are locked,” Microsoft explained. While not exposing plaintext data, it could impact memory integrity. Fixes for Azure Confidential Computing clusters are still in progress. The issue was disclosed by AMD and discovered by Benedict Schlueter, Supraja Sridhara, and Shweta Shinde of ETH Zurich.
CVE-2025-24052 – Windows Agere Modem Driver Elevation of Privilege Vulnerability
Similar to CVE-2025-24990, this flaw affects all supported Windows versions, even if the modem is inactive. “All supported versions of Windows can be affected by a successful exploitation of this vulnerability, even if the modem is not actively being used,” said Microsoft.
CVE-2025-2884 – Out-of-Bounds Read in TCG TPM2.0 Reference Implementation
This flaw could lead to information disclosure or denial of service in TPM 2.0. “CVE-2025-2884 is regarding a vulnerability in CG TPM2.0 Reference implementation’s CryptHmacSign helper function that is vulnerable to Out-of-Bounds read,” Microsoft stated. The issue was attributed to the Trusted Computing Group (TCG) and an anonymous researcher, with CERT/CC handling disclosure.
Microsoft’s October 2025 Patch Tuesday underscores the company’s continued focus on addressing critical and actively exploited vulnerabilities, even as it sunsets support for Windows 10.
U.S. cybersecurity firm F5 has confirmed that it suffered a cybersecurity incident involving a “highly sophisticated nation-state threat actor” that maintained long-term access to certain company systems.