A surge in supply chain attacks has put open-source software risk, prompting GitHub to strengthen security across its npm ecosystem. The company, which operates the world’s largest code repository, is moving quickly to block malware campaigns targeting developers worldwide.
“Open source software is the bedrock of the modern software industry. Its collaborative nature and vast ecosystem empower developers worldwide, driving efficiency and progress at an unprecedented scale. This scale also presents unique vulnerabilities that are continually tested and under attack by malicious actors, making the security of open source a critical concern for all,” wrote Xavier René-Corail on GitHub’s official blog.
Recent threats of npm attacks
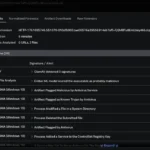
Threats to GitHub’s open-source software supply chain are coming in waves. September 2025 saw a rash of attacks, including the injection of malware into npm code packages and, most recently, a self-replicating worm known as Shai-Hulud worm that uses post-install scripts to hijack JavaScript-based npm packages.
Both of these attacks were the result of a traditional phishing campaign that was executed by unidentified hackers. Once the malicious actors gained access to user accounts, they were able to inject their code into seemingly normal and popular packages.
In the first attack, hackers injected malicious code into 18 npm packages; including some packages with weekly downloads numbering in the hundreds of millions. The second attack, which was approximately a week later, compromised even more packages. At the time of this writing, nearly 500 npm packages from multiple package maintainers have been compromised.
Bolstering security across the board
The team at GitHub has already laid out their plans to address these threats. Although an exact date hasn’t been announced, GitHub users can expect to see numerous changes in the near future.
Updates to GitHub authentication and publishing options include:
- Requiring two-factor authentication (2FA) for local publishing.
- Limiting the lifetime of granular tokens to seven days.
- Implementing a “Trusted Publishers” program for all package repositories.
Apart from authentication and publishing, GitHub will make more changes across the platform, including:
- Deprecating legacy classic tokens for all users.
- Deprecating time-based one-time password (TOTP) 2FA and requiring 2FA based on the standards of the Fast Identity Online (FIDO) Alliance.
- Shortening the expiration of granular tokens that have publishing permissions.
- Disallowing tokens by default.
- Eliminating the option to bypass 2FA for local publishing.
- Increasing the number of providers that are eligible for GitHub’s Trusted Publishers program.
In an effort to minimize workflow disruption, the team at GitHub will be introducing these changes gradually. They’re also committed to making the process as easy as possible for current users by providing timelines, updated documentation, and technical support over the coming days, weeks, and months.
GitHub CEO Thomas Dohmke recently stepped down after steering the company through a pivotal era of developer growth and AI integration. See how this leadership change could influence the platform’s next chapter.