Hackers have infiltrated the computer of a North Korean government spy, stealing and leaking 8.9 GB of secret files, including emails, passwords, and documents exposing links to Chinese hackers. The unprecedented breach lays bare sensitive details of North Korea’s cyber operations.
The hackers, known as Saber and cyb0rg, detailed the break-in in the latest issue of Phrack magazine, distributed at the DEF CON conference in Las Vegas. Their report outlines the theft of data from a member of Kimsuky, a state-sponsored espionage group, revealing stolen tools, internal manuals, and classified information.
1
Semperis
If your Active Directory isn’t secure, nothing is. Avoid single points of failure with comprehensive hybrid AD protection. Modernize your AD. Get lifecycle defense for identity-based attacks before, during, and after an attack, all supported by a dedicated incident response team.
2
ESET PROTECT Advanced
Protect your company computers, laptops and mobile devices with security products all managed via a cloud-based management console. The solution includes cloud sandboxing technology, preventing zero-day threats, and full disk encryption capability for enhanced data protection. ESET Protect Advanced complies with data regulation thanks to full disk encryption capabilities on Windows and macOS. Get started today!
3
NordLayer
The importance of cybersecurity rises with the growing numbers of cyber-attacks and malicious activities businesses face every second. Securing the data and constantly mitigating external threats like malware, phishing, or unfiltered websites is a challenge easier to overcome with advanced solutions. NordLayer is designed and developed with Secure Access Service Edge (SASE) architecture and Zero Trust model in mind to adhere to the most comprehensive and contemporary security landscape.
A state spy exposed
The target was no ordinary spy, but a working operative inside Kimsuky, a North Korean advanced persistent threat (APT) unit the hackers called “Kim.” On his computer, Saber and cyb0rg say they found the instruments of state espionage: malicious software, network infiltration tools, and code designed to pierce secure systems.
Mixed among the digital weaponry were traces of the man behind the screen, from browsing histories to files transferred between his Windows and Linux machines. He regularly visited popular hacking forums, followed open-source coding projects, and paid for multiple VPN services to mask his online activity. Records also showed he had remotely logged into other computers on his network.
Even his careful operational security could not keep the trove from being revealed in Phrack.
South Korea targeted
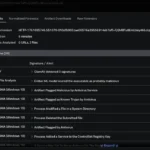
The files taken from Kim’s computer contained logs of active phishing campaigns against South Korea’s Defense Counterintelligence Command and other government agencies. Some of the attacks had taken place just three days before the breach.
The logs listed targeted email addresses, server details, and tools used to trick victims into handing over credentials. According to the hackers, the campaigns redirected targets through convincing fake websites before bouncing them to real government portals, making the theft harder to detect.
Also among the recovered data was the complete source code for Kebi, the South Korean Ministry of Foreign Affairs’ official email platform. The archive included every major component of the system, from the core code to its web, mobile, and administrative interfaces.
Timestamps suggest the material was taken very recently. As a critical channel for South Korea’s diplomatic communications, Kebi’s exposure could compromise sensitive government correspondence and internal operations.
Was China in on it?
Clues buried in the breached data point east. The operative’s browsing history included Chinese-language hacking sites and forums, along with visits to Taiwanese government and military pages viewed through online translation tools. He also used Google Translate to turn technical error messages into Chinese.
The patterns raise the possibility of operational overlap between Chinese and North Korean hackers. But without independent confirmation, it remains unclear whether this shows active cooperation, shared resources, or simply one operative drawing on widely available Chinese-language tools.
While any role by Chinese counterparts remains uncertain, Pyongyang’s hackers have been far from idle. Recent months have brought campaigns ranging from cryptocurrency theft attempts to custom malware aimed at high-value tech targets.
Read our coverage of a laptop farm scam in which North Korean operatives used stolen identities and remote-controlled tech to infiltrate American companies and steal corporate data.