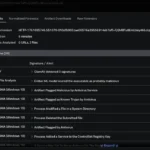
LLMNR / NBT-NS Spoofing Attack LLMNR / NBT-NS spoofing attackhow to use LLMNR & NetBIOS poisoning to capture credentials from the network using Kali + Responder.py and how to fix LLMNR & NBT-NS (NetBIOS) spoofing / poisoning attacks. Introduction A LLMNR & NBT-NS Spoofing Attack is a classic internal network attack that still works today, due to low awareness and the fact it’s enabled by default in Windows. This document explains what a LLMNR & NBT-NS attack is, how to use the attack when performing pen testing services and how to secure networks against the vulnerability. [clickToTweet tweet=”Check out the LLMNR Spoofing Guide by @AptiveSec #infosec #pentesting” quote=”Check out the LLMNR Spoofing Guide by Aptive”] What is LLMNR & NetBIOS Name Server Broadcast? When a DNS name server request fails Microsoft windows systems use Link-Local Multicast Name Resolution (LLMNR for short) and the Net-BIOS Name Service (NBT-NS) for fallback name resolution. What’s the issue with LLMNR & Netbios NS Broadcasting? If the DNS name does not resolve, the client performs a unauthenticated UDP broadcast to the network asking if any other system has the name it’s looking for. The fact this process is unauthenticated and broadcasted to the whole network allows any machine on the network to respond and claim to be the target machine. What is a LLMNR / NBT-NS Poisoning Attack? By listening for LLMNR & NetBIOS broadcasts it’s possible to masquerade as the machine (spoof) the client is erroneously trying to authenticate with. After accepting the connection it’s possible to use a tool like Responder.py or Metasploit to forward on requests to a rogue service (like SMB TCP: 137) that performs the authentication process. During the authentication process the client will send the rogue server a NTLMv2 hash for the user that’s trying to authenticate, this hash is captured to disk and can be cracked offline with a tool like Hashcat or John the Ripper (TJR) or used in a pass-the-hash attack. LLMNR and NBT-NS are enabled by default in Windows and with awareness of this attack being fairly low you stand a good chance of being able to gather credentials on an internal network. Leave Responder.py running during an engagement while you’re working other attack vectors. What about Linux & Apple clients, are they Vulnerable? Yes, Linux and Apple clients use a similar protocol called multicast DNS or mDNS for short which listens on TCP: 5353. For more information on mDSN see the mDNS wikipedia page Typical LLMNR / NetBIOS Name Server Attack The diagram below shows the typical scenario for this type of attack where a user mistypes a server name. Step-by-step LLMNR / NBT-NS Poisoning Attack User sends incorrect SMB share address SNARE01 DNS Server responds with SNARE01 – NOT FOUND Client performs LLMNR / NBT-NS broadcast Responder tells the client it’s SNARE01 and accepts the NTLMv2 hash Responder sends an error back to the client, so the end user is non the wiser and simply thinks they have the wrong share name Practical […]
Recent Posts
- GovWare 2025 Security Operations Centre
- GovWare 2025 Security Operations Centre
- From Detection to Deep Dive: Splunk Attack Analyzer and Endace for GovWare 2025 Security
- From Detection to Deep Dive: Splunk Attack Analyzer and Endace for GovWare 2025 Security
- Unmasking Attacks With Cisco XDR at the GovWare SOC